What Are The Best Identity Theft Protection Services

Co-ordinate to the Federal Trade Commission's "Consumer Sentinel Network Data Book," the most common categories for consumer complaints in 2021 were:
- Identity theft
- Imposter scams (a subset of fraud)
- Credit bureaus, information furnishers and study users
"Regime documents or benefits fraud" was the almost prevalent blazon of identity theft example — more than 395,000 people reported that someone submitted a fraudulent government document under their name.
Equally the COVID-19 pandemic continues in 2022, the FTC as well continues to transport out warnings of scams targeting Americans working and studying from home.
Similar warnings come from the business sector too. "When you are working from abode, you are not behind the castle walls anymore," said John Hammond, a cybersecurity researcher at the security house Huntress. "You are working with your own devices, away from the safe perimeter of corporate networks."
This situation creates an easier and more lucrative path for attackers to launch ransomware. From 2019 to 2020, the U.Due south. experienced a 311% increase in victims, with a full payout of $350 million. Global ransomware attacks then almost doubled in 2021 compared with 2020, increasing by 93%, according to the NCC Group's 2021 Annual Threat Report.
Sophos' State of Ransomware study showed a similar tendency, with 66% of the organizations surveyed seeing ransomware attacks in 2021. For context, merely 37% of respondents reported that they were hit by ransomware attacks in 2020. Experts believe i of import contributing cistron to the popularity of this kind of assault is the number of people still working from home.
The FTC continues to advise consumers to be wary of cybercriminals exploiting coronavirus fears to steal personally identifiable information (PII). Fiscal data and medical information are especially susceptible right now.
Register for the costless FTC Consumer Alerts blog to keep up with recent tips, advice and scams.
Cybersecurity and COVID-19
According to the FTC, fraudsters are still at work creating scams perpetuating virus-related fear. Texts and robocalls apropos vaccines, COVID-19 cures and antibody tests are prevalent. Some scammers are even impersonating FTC staff to tempt people with nonexistent awards or funds related to the pandemic.
The U.S. Department of Justice shut down hundreds of artificial websites in the kickoff twelvemonth of the pandemic, simply plenty are all the same active. These sites are frequently disguised as government agencies or humanitarian organizations and promise coronavirus tests, relief payments or outright cures.
They await legitimate, so information technology's easy to click, simply a click provides hackers the ways to commencement phishing email campaigns and implant malware, all in an endeavor to go personal and private information.
For example, a link that seems like it should lead you lot to a map of "COVID-19 cases near me" could infect your phone or reckoner with spyware or ransomware. Call up to visit the Centers for Disease Control and Prevention or World Health System for condom, accurate information nearly coronavirus trends and statistics.
According to the U.Southward government, the IRS and Equifax, common COVID-19-related scams in 2021 included:
- Economic bear upon payment theft
- Scammers impersonating government officials
- Commitment scams
- Fake COVID testing, vaccine and handling scams
- Unemployment benefits fraud
- Simulated charities made to look like real charities that deal with the COVID-19 pandemic
5 cybersecurity tips for working from habitation
Now that more Americans are working from home indefinitely, we asked the ConsumerAffairs Data Security team for some tips on how to stay safe online.
For more on how to keep your devices safe while socially distancing or sheltering in place, the ConsumerAffairs Information Security team recommends visiting sans.org and staysafeonline.org.
- Secure your home network: Potent passwords and encryption are the best ways to secure your home network. Alter your default administrator password before a hacker discovers you lot've left it set to the manufacturer's default. Use WPA2 or WPA3 encryption so hackers can't read the information y'all send. For more guidance, read nearly securing your wireless network.
- Limit access to your work device: Avoid giving anyone an opportunity to view confidential textile without your dominance. Exist sure to shut downwards or lock your work reckoner when you aren't around. It'southward too like shooting fish in a barrel for friends and family to accidentally erase, modify or infect data on your device.
- Be careful where yous click: Always hover over links before you click them to make sure the hyperlink is the same as the link-to address. Be extra cautious about emails from unknown people, especially if they seem random, illogical or threatening.
- Be skeptical of job offers: Cybercriminals use bogus employment posts to trick people into money laundering schemes ("coin mules") and collect their PII or fiscal information. Remote freelancers could be especially vulnerable.
- Protect your devices: If yous haven't already, ensure that your antivirus and anti-malware software is up to date.
Identity theft trends in 2022
In its 2021 Annual Data Breach Report, the Identity Theft Resource Center (ITRC) reported that 1,862 data compromises occurred in 2021, breaking the previous record of 1,506 set in 2017.
Co-ordinate to a subsequent Information Breach Analysis from the ITRC, in that location were xiv% more than reported information compromises in the offset quarter of 2022 than in the kickoff quarter of 2021. This is the third year in a row during which the number of overall data compromises increased in comparison to the previous year's initial quarter.
"The fact the number of alienation events in Q1 represents a double-digit increase over the same time terminal twelvemonth is another indicator that data compromises will proceed to ascent in 2022 after setting a new all-time loftier in 2021," Eva Velasquez, President and CEO of the ITRC, stated on the organization's website. "Information technology is vital everyone continues to exercise good cyber-hygiene, businesses and consumers, to assist reduce the corporeality of personal information flowing into the hands of cyberthieves."
Phishing and ransomware remain the top root causes of data compromises. The health intendance, financial services, manufacturing/utilities and professional services sectors experienced the about compromises in the beginning quarter of 2022.
Some of these attacks have get national news and impacted major companies. Although these breaches may not directly target consumers, they do touch their daily lives.
Cyberattacks are more aggressive
Co-ordinate to the CrowdStrike 2022 Global Threat Written report, e-criminal offence groups are yet the primary source of attacks, making up nearly one-half of all observed criminal cyberactivity in 2021.
Withal, there is a growing trend of targeted cybercrime, defined in the report as "state-sponsored intrusion action that includes cyber espionage, state-nexus destruction attacks and generating currency to support a government."
Assaults on U.Southward. infrastructure
The infamous SolarWinds hack began in 2020 but had repercussions that carried into 2021, and this was followed past the Colonial Pipeline breach, signaling a larger tendency of hackers targeting U.Southward. infrastructure.
The infamous SolarWinds hack began in 2020 but had repercussions that carried into 2021, and this was followed by the Colonial Pipeline breach, signaling a larger trend of hackers targeting U.S. infrastructure.
Every bit a response to these growing threats, President Joe Biden issued an executive society on improving the state'due south cybersecurity and earmarked $nine.8 billion of the 2022 federal budget for civilian cybersecurity activities, such as the It systems and networks used by the federal authorities. In this budget plan, the Department of Defense receives a separate $four.3 billion for its own cyber operations, and an boosted $4.3 billion was allocated to providing local grants for private infrastructure that impacts the everyday lives of Americans.
Internet of Things threats are on the rise
In the get-go one-half of 2021, Internet of Things (IoT) devices saw more than twice as many cyberattacks equally they had in the first half of 2020, co-ordinate to the cybersecurity house Kaspersky.
"IoT vulnerabilities accept been discovered and exposed across many industries," wrote Oleksii Tsymbal, Chief Innovation Officer at MobiDev. "These vulnerabilities threaten sensitive data as well every bit personal safety. Without a incertitude, the Internet of Things is a prime target for hackers in 2022, and whatsoever organization that produces or uses these devices needs to be prepared."
Just considering IoT devices are small does non mean cybercriminals care for them equally unimportant. The best advice is to update your devices continually and modify passwords oftentimes.
Formjacking has been around for a while, but it's still in apply
In 2021, cybercriminals nevertheless employed formjacking as a means to have in millions of dollars each month past hijacking credit card information from online payment forms. It pays to be vigilant when making purchases online by making certain you are familiar with the company you're buying from.
Ransomware is a serious threat in 2022
Ransomware payouts increased dramatically in 2021, with ane case reportedly causing the victims to pay out an astonishing $50 million. To incentivize the victim to pay, these cybercriminals utilise deprival-of-service (DoS) attacks and threaten to sell or release sensitive data to the public.
Not only is at that place a rising in these types of attacks, but the FBI reports there are 100 ransomware variants making their way around the world.
New business relationship fraud is alive and well
A report from Javelin Strategy & Inquiry showed a 109% increase in new business relationship fraud in 2021. This blazon of fraud generally works in one of two means.
In the first method, cybercriminals might apply stolen documents to fix up new accounts. They and so get the money and run, leaving the victim to face the consequences.
Alternatively, after they accept set up a new account, cybercriminals sometimes behave for a twelvemonth or and so, remaining undetected. Then, after increasing credit limits or obtaining new credit cards because of their "stellar" payment history, they will max out the accounts and disappear.
Account takeovers are a major issue
Business relationship takeover fraud is a type of identity theft in which hackers take control of a legitimate individual's digital identity for financial proceeds.
According to a 2021 written report, 43% of U.S. merchants claimed business relationship takeover fraud deemed for over 10% of chargebacks, and separate enquiry has reported that 22% of U.S. adults have been victims of account takeovers.
Deepfakes are getting more advanced
A single photograph and the correct software allow a cybercriminal to create a imitation merely realistic image or video when overlaying that photograph with some other image or video. This kind of impersonation is an up-and-coming class of fraud that is finding its way onto social media platforms. So, beware of fake photos and videos, especially on social media.
The potential to politically manipulate populations with the utilise of deepfakes on Idiot box or on the internet could as well lead to an increase in political instability beyond the globe.
Record-breaking cryptocurrency theft
In March 2022, Ronin Network was hacked and robbed of cryptocurrency worth $540 million at the time. The hackers got away with approximately 173,600 ethers (units of the widely used ethereum cryptocurrency) and over 25 meg USDC (a cryptocurrency that is pegged to the U.S. dollar).
Based on the value of these cryptocurrencies at the time of the theft, this incident would be the 2d-largest cryptocurrency heist nosotros know of. All the same, given the amount the stolen avails appreciated earlier the hack was discovered, many have identified this as the largest cryptocurrency theft ever.
Increased attempt to solve the year 2038 problem
Similar to the Y2K trouble, the 2038 problem is a problems that will affect the way computers store time stamps. Computer logic defines time stamps with the current date and time, minus the number of seconds that have passed since Jan. 1, 1970.
In 2038, the number of elapsed seconds will exceed the data that can be stored in a four-byte data blazon, meaning most computers volition need an actress byte to preserve their timing systems.
For many, the 2038 problem is solved. Others sense that a solution is near and there volition exist no threat by the fourth dimension 2038 arrives. Without a resolution, however, hackers will likely search for ways to exploit this bug.
Who is about at gamble for identity theft?
Nigh identity thefts are crimes of opportunity. Identity thieves oft target those who don't regularly check for identity theft warning signs and are unlikely to report irregular activity on their credit reports. This means that several groups are especially vulnerable to identity theft.
Children and seniors
Everyone with a Social Security number is at risk for identity theft, simply two demographics get targeted aggressively and often: the very young and the very one-time.
- Children are targeted because identity thieves can use a kid's Social Security numbers to constitute a fraudulent "clean slate." Identity theft experts recommend parents monitor their kids' credit reports to check for identity theft equally often as their own.
- Seniors are targeted most often over the telephone and through internet phishing scams. Some studies suggest that people go more than trusting as they age, which explains why it's more difficult for older adults to discover fraudsters.
Members of the military
While deployed, active-duty members of the armed forces are particularly vulnerable to identity theft because they may non notice mistakes on their credit reports or receive calls from debt collectors regarding a fraudulent charge. According to FTC reports, military consumers are most afflicted by government documents or benefits fraud and credit card fraud.
- There were 17,407 total military consumer authorities documents or benefits fraud reports in 2021.
- At that place were 9,379 total military consumer credit card fraud reports in 2021.
- Military consumers' reports of depository financial institution fraud increased by roughly 8.4% betwixt 2020 and 2021.
- Armed services members are also increasingly affected by loan or lease fraud.
2021 military consumer loan or lease fraud reports
Repeat victims
People who accept previously been afflicted by identity theft are at a greater take a chance for future identity theft and fraud. "Iii out of every ten people tell us this happened to them before and at present they're dealing with information technology once again," said the ITRC's Velasquez.
For more information well-nigh how victims of identity theft can protect themselves from future fraud, read about the identity theft recovery procedure.
The deceased
Identity thieves can target the recently departed with information gleaned from public obituaries and access the deceased'due south Social Security number through the Social Security Administration's master files.
Stealing a expressionless person'south identity is unremarkably referred to as "ghosting." Ghosting often goes unnoticed by surviving family members for months or years.
Where is identity theft most mutual?
The FTC collects reports from consumers on a range of marketplace experiences and stores them in a secure online database. FTC statistics also include reports from other organizations, including federal, country, local and international law enforcement agencies. Out of over 5.7 million reports last twelvemonth, slightly more than than 25% were related to identity theft.
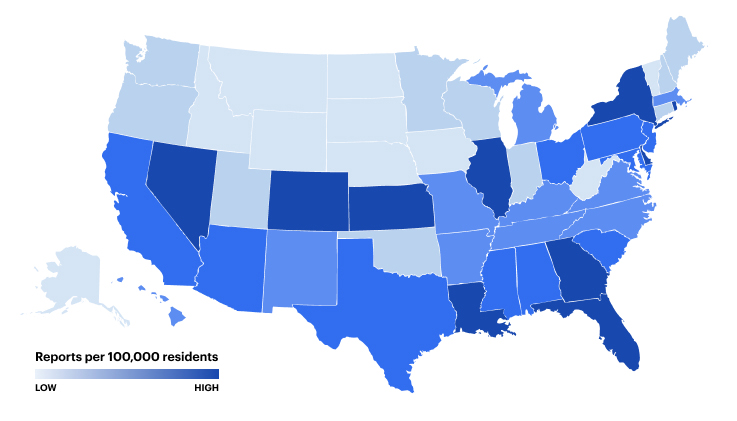
According to the FTC, in 2021, Rhode Island had the highest charge per unit of identity theft reports per capita, merely Texas had the highest total number of reports overall.
Identity theft statistics by state
Top 10 metropolitan statistical areas for identity theft reports
Bottom line
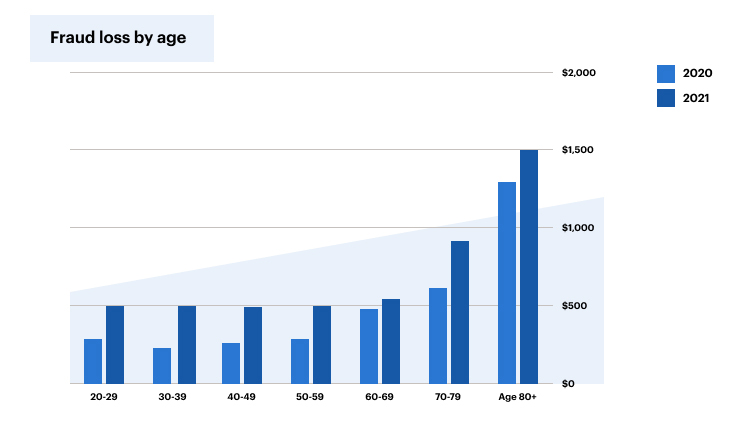
Anyone with a Social Security number can exist the bailiwick of identity theft, but according to the FTC's 2021 Sentinel Information Volume, published in February 2022, the most targeted victims are between the ages of 60 and 69. We can't completely eliminate identity theft, but people who regularly monitor their accounts, bills and credit reports can lower their take chances.
If you think you're a victim of identity fraud, work with the FTC to restore your accounts and become on the road to recovery.
Identity theft terms
The better people empathize identity theft, the more equipped they are to protect themselves. Our identity theft glossary below is regularly updated to include the most contempo identity theft terms in the news.
- Account takeover: An business relationship takeover is when a fraudster uses personal information to obtain products and services. Credit menu fraud is the most rampant, but skimming and phishing are as well common types of account takeovers.
- Anti-virus: Anti-virus software runs continuously in the background of a computer and scans for viruses, worms and malware every time the user accesses a website or downloads anything.
- Allurement and switch: A allurement and switch set on is when a hacker buys advertizing infinite on a webpage and so links the advertisement to a page infected with malware.
- Blackness hat hacker: All hackers are capable of compromising computer systems and creating malware, merely black lid hackers use these skills to commit cybercrimes.
- Blockchain: A blockchain is a string of fourth dimension-stamped digital records shared between multiple computers. If the data in one block changes, all subsequent blocks in the blockchain reflect the alteration and become invalid. Blockchains help preclude identity theft and fraud past making it difficult to tamper with the information in a block.
- Bot: Brusque for "robot," a bot is an autonomous program that interacts with estimator systems in a way that appears or attempts to appear human. Hackers can apply bots to mine for usernames and passwords used to commit identity fraud.
- Cookie theft: Cookie theft is when a cybercriminal makes copies of unencrypted session information and so uses that data to impersonate someone else.
- Credential bully: Credential smashing describes the various methods — word lists, guessing and brute-force — cybercriminals use to obtain passwords. Credential cracking threats are why it'southward of import to create varied and complicated passwords for all accounts.
- Criminal impersonation: Someone commits criminal impersonation when they assume a fake or false identity, usually for political or financial proceeds.
- Cybersquatting: Also sometimes called domain squatting, cybersquatting is when a domain name is stolen or misspelled to attract users for exploitation or turn a profit.
- Cryptovirology: Cryptovirology is the study of how cryptology is used to create dangerous malware.
- Data breach: A data breach is when individual or confidential data is released to an untrusted environment. Cybercriminals can infiltrate a information source physically or remotely featherbed network security to expose passwords, banking and credit information, passport and Social Security numbers, medical records and more.
- Dark web: The night spider web, also known as the deep web or invisible spider web, is a office of the internet that'south non attainable through standard search engines such as Google or Bing. Information technology's often accessed through Tor Browser software, which keeps visitors anonymous and untraceable. It'southward not illegal to be on the nighttime web, but many illegal transactions occur on the nighttime spider web (such as buying credit card or Social Security numbers).
- Deprival-of-service attack: A denial-of-service (DoS) assault potentially causes a victim's server or network to go overwhelmed with traffic, resulting in a denial of service to legitimate traffic. At this bespeak, the victim'southward data is also locked or is under threat of a leak. The victim is pressured to pay to cease the attack and regain control of their information.
- Distributed deprival-of-service set on: A distributed denial-of-service (DDoS) set on uses a network of distributed computers to direct junk traffic at the targeted website.
- Encryption: Encryption is a manner to scramble data using estimator algorithms to prevent unauthorized access to data or sensitive information.
- Firewall: In computing, a firewall is a software programme that blocks unauthorized users from getting in without restricting outward communication.
- Formjacking: Formjacking is when a hacker infiltrates an e-commerce checkout page to steal credit card information. It's similar to ATM skimming for the internet age.
- Ghosting: In the context of identity theft, ghosting refers to when someone steals the identity of a dead person.
- Greyness lid hacker: Grey lid hackers' ethics are somewhere between black and white lid hackers. Grey lid hacking involves illegal cyberactivity, but the hacker often reports vulnerabilities to the system'south possessor and requests a fee in commutation for the information — if a system'southward possessor does non comply with their request, the grey hat hacker usually exploits the newly discovered cybersecurity vulnerability.
- Honeypot: A honeypot is a decoy target used to mitigate cybersecurity risks or get more data about how cybercriminals work.
- Identity cloning: Identity cloning is a type of identity theft in which a fraudster assumes someone else's identity and attempts to live under that assumed identity.
- Identity score: Like to a credit score, an identity score is a system that gauges an individual'south data for legitimacy.
- Imposter scam: Imposter scams involve a fraudster posing every bit a different person for financial or political gain. Normally, the imposter tricks others into giving them money through email, over the phone or via online dating services.
- Net of Things: The Net of Things, or IoT, describes the interconnectedness of all devices that access WiFi, including cell phones, cameras, headphones and an increasing number of other objects, including washing machines and thermostats.
- Keylogger: A keylogger is a computer program that records a person's keystrokes to obtain confidential information.
- Malware: A portmanteau of "malicious" and "software," malware describes any software created with the specific intent to cause disruption or impairment. Trojans, bots, spyware, worms and viruses are all types of malware.
- Passive attacks: Whatsoever network attack where the organization is monitored or scanned for vulnerabilities is considered "passive attack" because the targeted data isn't modified or damaged.
- Pharming: Sometimes chosen "phishing without a lure," pharming is a type of scam where malicious code is installed onto a device or server to misdirect users onto illegitimate websites.
- Phishing: Phishing is a popular type of internet scam in which fraudsters send emails claiming to be from a reputable company to fob individuals into revealing personal information. Phishing attacks more than doubled from 2019 to 2020, from 114,702 incidents to 241,324 incidents.
- Physical identity theft: Dissimilar wireless identity theft, physical identity theft requires an identity thief to exist in close proximity to their target. Examples of physical identity theft include stealing a wallet or computer, dumpster diving and postal mail theft.
- Proxy server: A proxy server establishes a substitute IP (Internet Protocol) address identity. When you connect online, your calculator's IP address is transmitted to websites and establishes your location and may give other identifying details. Proxy servers allow users to connect to the cyberspace anonymously and featherbed blocked or restricted websites.
- PowerShell: An automated chore framework by Microsoft, PowerShell tin can be embedded in applications to automate batch processing and systems management tools.
- Ransomware: Ransomware is a type of malware that threatens to betrayal or block an individual'south or business organisation' data unless a bribe is paid.
- SIM bandy scam: Sometimes called a port-out scam or SIM splitting, a SIM bandy scam is a circuitous type of jail cell telephone fraud that exploits two-gene hallmark to access data stored on someone's cell telephone. Put only, if a fraudster has your telephone number, they tin call your phone visitor and inquire to have the number transferred to "your" new phone. The fraudster so has access to all of your accounts that use two-factor authentication.
- Skimming: Skimming is a type of credit card fraud in which the victim'southward account numbers are copied and transferred to a counterfeit bill of fare.
- Smishing: Similar to phishing, smishing (or SMS phishing) is when someone attempts to mine sensitive information under a fake identity through text messages.
- Sockpuppet: Sockpuppetting is when a person assumes a false identity on the cyberspace for the purpose of deception.
- Spoofing: A spoofing assail is when an illegitimate website falsifies information to announced equally a trustworthy website to visitors.
- Spyware: Spyware is any software designed to get together data from an individual or enterprise. The four main types of spyware are adware, Trojan horses, tracking cookies and system monitors.
- Constructed identity theft: Synthetic identity theft is when a criminal combines stolen and false information to create a new, fraudulent identity.
- Organisation monitor: Much like information technology sounds, a organisation monitor is an application that surveils computer activeness. System monitors usually run unnoticed and can record passwords, chats and emails, websites visited and other sensitive or identifying data.
- Tracking cookie: Websites apply tracking cookies to gather and share data from their visitors. Unlike malware, tracking cookies won't harm computer systems, but they can create privacy concerns. Google has stated it intends to eliminate the employ of 3rd-party cookies past the end of 2023.
- Trojan horse: Like its classical namesake, a Trojan horse is a blazon of malware disguised to appear similar prophylactic software. Cybercriminals use Trojans to access sensitive data and gain access to individual systems.
- Waterhole set on: A waterhole attack occurs when a hacker targets a specific group or community. The hacker infects an individual within the targeted group with malware in an attempt to infect the entire grouping.
- Wireless identity theft: Also sometimes chosen contactless identity theft or RFID identity theft, wireless identity theft is committed by wireless mechanics. Examples of wireless identity theft include phishing and spoofing.
- Whaling: Whaling is a phishing set on that targets loftier-level employees within a visitor to steal confidential information or sensitive information.
- White hat hacker: Unlike a blackness chapeau hacker, a white lid hacker uses their power to intermission computer networks or bypass security protocols for adept rather than evil. White hat hackers are oftentimes employed by governments or companies to perform vulnerability assessments.
- Worm: A worm is a type of malware that self-replicates and spreads from figurer to computer.
- Virus: Similar to worms, viruses make copies of themselves. The main difference between viruses and worms is that viruses crave a host plan to spread.
- Vishing: Like phishing or smishing, vishing is when an identity thief attempts to proceeds sensitive information over the phone.
- Cypher-day exploit: A zero-24-hour interval exploit is when cybercriminals target a software the same 24-hour interval weakness in that software is discovered and earlier a patch tin can be released to fix the vulnerability.
Did you find this article helpful? |
What Are The Best Identity Theft Protection Services,
Source: https://www.consumeraffairs.com/finance/identity-theft-statistics.html
Posted by: eppsdiesequan49.blogspot.com


0 Response to "What Are The Best Identity Theft Protection Services"
Post a Comment